LabVIEW as a Memory-Safe Language
Overview
NI LabVIEW is a graphical programming platform widely used for data acquisition, instrument control, and test automation. While memory-safety vulnerabilities plague many traditional software environments, LabVIEW stands out by virtue of its architecture and design principles. This white paper explores the mechanisms and features that make LabVIEW a memory-safe language (MSL), how these attributes compare to conventional programming languages, and the implications for developers seeking robust, reliable, and secure applications.
Memory safety is a critical aspect of software security and reliability. Classic memory-safety issues such as buffer overflows, use-after-free errors, and dangling pointers are responsible for a significant portion of software defects and security vulnerabilities in languages like C and C++.1 LabVIEW, by contrast, abstracts away many of these risks through its high-level, dataflow-driven graphical environment.
Contents
- Understanding Memory Safety and Its Importance
- LabVIEW’s Memory Model
- Comparative Analysis: LabVIEW Memory Safety vs. Traditional Languages
- Benefits of Using LabVIEW for Secure Applications
- Buffer Overflow Prevention
- Potential Limitations and Best Practices
- LabVIEW Helps Developers Build with Confidence
- Next Steps
Understanding Memory Safety and Its Importance
Memory safety refers to the assurance that a program accesses memory in a well-defined, predictable manner. This feature helps prevent corruption, leaks, and writing data outside of intended bounds. These memory issues can cause crashes and undefined behavior. Worse, threat actors manipulate memory issues to execute arbitrary code, turning memory bugs into significant security vulnerabilities. Concerns over memory safety include the following types of issues:
- Buffer overflows—Writing outside the boundaries of allocated memory.
- Dangling pointers—Accessing memory that has already been freed.
- Use-after-free—Using pointers to memory locations after they have been deallocated.
- Memory leaks—Failing to release memory, causing gradual resource exhaustion.
Languages that provide direct memory access (for example, by using pointers) are especially susceptible to these issues. Memory-safe languages, in contrast, either restrict or completely abstract direct memory management from the developer.
LabVIEW’s Memory Model
Fundamentally, LabVIEW is different from traditional text-based languages. Its graphical programming paradigm is based on dataflow principles, where the execution of code is determined by the flow of data between nodes (called Virtual Instruments, or VIs).
The following aspects of LabVIEW’s inherent architecture promote memory safety:
- No direct pointer manipulation—LabVIEW does not expose memory addresses or pointers to the developer.
- Automatic memory management—LabVIEW allocates and deallocates memory for variables, arrays, and structures as needed.
- Type safety—The LabVIEW environment enforces strong typing at edit-time and runtime.
- Immutable wire values—Once data enters a wire (the graphical equivalent of a variable), it cannot be altered unexpectedly elsewhere in the program.
- Reference counting and garbage collection—LabVIEW manages data lifetimes, ensuring memory is automatically reclaimed when no longer used.
Dataflow Paradigm and Its Impact
In LabVIEW, programs are constructed by connecting functional blocks with wires that carry data. Each block executes only when all required inputs are available, and data locations cannot be accessed before the data is produced, avoiding memory race conditions.
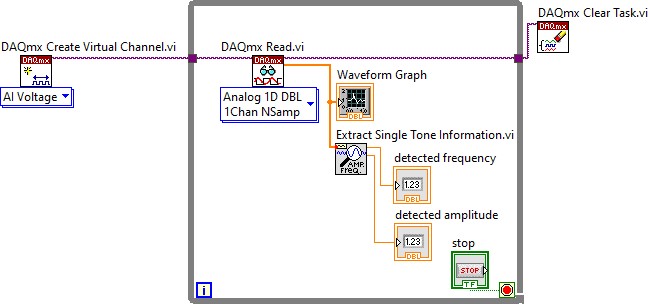
Figure 1. LabVIEW Code Example
This model naturally avoids many programming errors that arise from the improper sequencing of operations in imperative languages.
Memory Allocation and Management
The LabVIEW Run-Time Engine is responsible for all memory allocation and deallocation. Developers never need to manually request or free memory, removing the risk of leaks and use-after-free errors. When arrays or clusters (struct-like data) grow or shrink, LabVIEW transparently manages the associated memory. For example, if a developer creates a loop that builds up an array, LabVIEW automatically resizes the array and manages the associated memory space. When the array variable goes out of scope, LabVIEW’s garbage collector reclaims the memory.
Strong Typing and Boundary Checking
The LabVIEW development environment performs rigorous type-checking during VI compilation and execution. Attempts to wire incompatible data types together are caught at edit-time, preventing runtime errors. Additionally, array and string operations include boundary checking to prevent buffer overflows.
Absence of Low-Level Memory Control
One of the most effective safeguards is the absence of low-level memory control: LabVIEW does not provide any mechanism for the user to perform arbitrary pointer arithmetic or access memory directly. This design means that vulnerabilities common in C or assembly—such as stack or heap overflows—are not possible in native LabVIEW code.
Comparative Analysis: LabVIEW Memory Safety vs. Traditional Languages
To better understand LabVIEW’s memory safety, it is instructive to compare it to languages like C, C++, and even Java or Python.
- C/C++—These languages provide direct memory access, require manual memory management, and are susceptible to a wide range of memory safety errors. CISA recommends against using C/C++ for new projects.
- Java/Python—These languages provide automatic memory management, but still allow some indirect memory errors. For example, many underlying Python modules are written in C, and bugs in these modules can lead to memory issues in the Python application. Python also doesn’t enforce memory safety rules at runtime like other true MSLs do.
- LabVIEW—LabVIEW provides no pointers, and uses strict typing, with fully managed memory, significantly reducing the attack surface and risk of errors. LabVIEW does allow the user to call DLLs written in C/C++, which may introduce memory issues.
In summary, LabVIEW’s design eliminates entire categories of memory-related vulnerabilities (e.g., buffer overflows) and simplifies secure application development, offering a significant advantage over traditional languages like C andC++., with similar protection to Python and Java.
Benefits of Using LabVIEW for Secure Applications
Memory safety in LabVIEW has tangible benefits for developers, organizations, and end-users:
- Reduced risk of security vulnerabilities—Eliminating buffer overflows and pointer misuse closes off many common attack vectors.
- Higher reliability—Applications are less likely to crash due to hard-to-find memory errors.
- Faster development—Developers can focus on application logic without worrying about memory allocation or deallocation bugs.
- Easier maintenance—LabVIEW code is less prone to subtle, low-level errors that can make debugging and maintenance costly and time-consuming.
- Safety-critical applications—Frequently, LabVIEW is used in environments where reliability is paramount, such as laboratory automation, industrial control, and scientific research.
Buffer Overflow Prevention
Traditional buffer overflows occur when data exceeds the boundaries of a fixed-length buffer, overwriting adjacent memory and potentially allowing arbitrary code execution. In LabVIEW, array and string operations are always bounds-checked. Attempts to write beyond the end of an array or string will result in a run-time error rather than silent memory corruption.
Potential Limitations and Best Practices
Like any memory-safe environment, understanding LabVIEW’s boundaries is important:
- External code integration—Calling external libraries (DLLs, shared libraries) from LabVIEW with the Call Library Function Node can introduce memory safety issues if those libraries are not themselves safe.
- Resource exhaustion—Infinite loops or uncontrolled memory allocation can still lead to memory exhaustion, though not corruption.
- Version compatibility—As LabVIEW evolves, certain behaviors (e.g., memory management optimizations) may change, requiring attention when upgrading or porting legacy code.
To maximize safety when calling external code, follow these best practices:
- Isolate Unsafe Code—Encapsulate unsafe library calls in a separate module or process. Use microservices or IPC (inter-process communication) to isolate memory-unsafe code. This way, a crash or memory corruption in the unsafe code doesn’t bring down the whole application.
- Validate Inputs and Outputs Rigorously—Memory corruption often stems from bad inputs or unexpected outputs. Validate all data passed to and from the unsafe library. Use bounds checking, null checks, and type assertions.
- Employ Static and Dynamic Analysis Tools—Use tools to catch memory issues early. Use LabVIEW’s static and dynamic memory tools, included with LabVIEW Professional, to test for memory issues.
- Minimize Unsafe Surface Area—Only expose the minimum necessary functionality from the unsafe library. Avoid passing complex data structures or pointers unless absolutely necessary. Keep the interface as simple and well-defined as possible.
- Audit and Monitor—Regularly audit external code called by the LabVIEW program.
LabVIEW Helps Developers Build with Confidence
LabVIEW’s design—based on a graphical dataflow paradigm, strong type checking, automatic memory management, and the absence of direct pointer manipulation—provides a highly memory-safe environment. Developers benefit from reduced risk of memory-related bugs, increased productivity, and the ability to build applications for demanding, safety-critical industries with confidence.
While no environment is entirely immune to errors—especially when interacting with unsafe external components—LabVIEW significantly raises the bar for memory safety compared to traditional text-based languages. For organizations seeking reliability and security in measurement, automation, and control applications, LabVIEW is a compelling choice for memory-safe development.
| Aspect | C/C++ | Python/Java | LabVIEW |
|---|---|---|---|
| Memory Access | Direct memory access | No direct memory access | No direct memory access |
| Memory Management | Manual memory management, prone to errors | Automatic memory management | Automatic memory management |
| Error Susceptibility | High risk of memory safety errors (e.g., buffer overflows) | Significantly reduced risk due to strict typing and managed memory | Significantly reduced risk due to strict typing and managed memory |
| Pointers | Extensive use of pointers, increasing complexity and risk | No direct use of pointers | No direct use of pointers |
| Security | High attack surface due to manual memory handling and susceptibility to buffer overflows | Minimal attack surface, immune to buffer overflows and pointer exploits | Minimal attack surface, immune to buffer overflows and pointer exploits |
1 "Memory Safe Languages: Reducing Vulnerabilities in Modern Software Development,” Cybersecurity and Infrastructure Agency, June 2025, https://www.cisa.gov/resources-tools/resources/memory-safe-languages-reducing-vulnerabilities-modern-software-development.
Java is a registered trademark of Oracle and/or its affiliates. Other names may be trademarks of their respective owners.