NI Linux Real-Time Security Update - November 2014
Overview
Contents
- Introduction
- Affected Targets
- Installing the Appropriate Software Patch
- Background
- Patch Details
- Additional Resources
Introduction
NI has released software patches for a security vulnerability that affects the NI Linux Real-Time operating system for the targets listed in the following table. Please review the installation instructions for each product family below. If you are using devices from two or more of the affected product families, complete the installation instructions for each applicable product family to ensure that all affected targets are patched.
Affected Targets
| Software Family | Target |
| CompactRIO | cRIO-9030 |
| cRIO-9031 | |
| cRIO-9033 | |
| cRIO-9034 | |
| cRIO-9038 | |
| cRIO-9066 | |
| cRIO-9067 | |
| cRIO-9068 | |
| NI 9149 | |
| sbRIO-9651 | |
| myRIO-1900 | |
| myRIO-1950 | |
| NI roboRIO | |
| Compact Vision System | CVS-1458RT |
| CVS-1459RT | |
| CompactDAQ | cDAQ-9132 |
| cDAQ-9134 | |
NI strongly recommends that you install this patch to fix this vulnerability if you have or intend to use one of the devices listed above.
Installing the Appropriate Software Patch
CompactRIO
Complete the following steps to ensure that any current or future devices have this security update included.
- Verify you have CompactRIO 14.0.1 or 14.1.0 installed on the host system. In Measurement & Automation Explorer (MAX), expand My System»Software and verify that CompactRIO 14.0.1 or 14.1.0 appears. You can choose to download the patch through NI Update Service or through the download page in the Additional Resources section.
- Install the NI Linux Real-Time Security Update for CompactRIO - November 2014 on your host computer. To verify a system has been patched you should see firmware revisions 2.2.0f0 in the following directory <Program Files>\National Instruments\Shared\Firmware\76D6\. Ensure that you have patched all development systems.
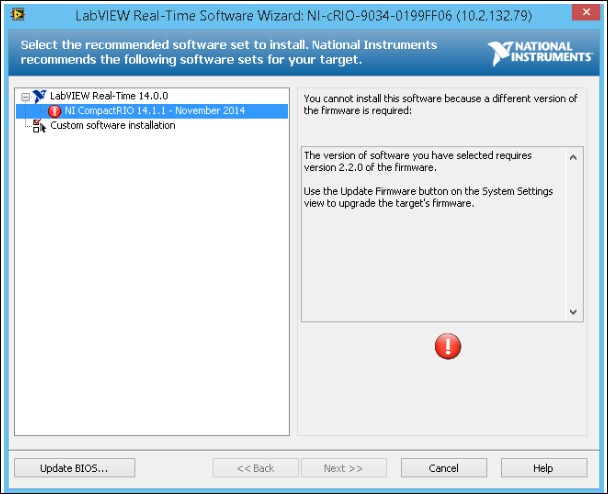
- Update the firmware on your affected controllers. Refer to Upgrading Firmware on my NI Linux Real-Time Device for directions on how to update the firmware on your current controllers. Updating the firmware patches the Safe Mode on the controller so the vulnerability cannot be used while in this mode. In MAX, click the System Settings tab of the controller and verify that Firmware Revision is 2.2.0f0 or later. If this step is skipped you will see the screen shot similar to figure below. The message should read "The version of software you have selected requires version 2.2.0 of the firmware. Use the Update Firmware button on the System Settings view to upgrade the target's firmware."
- Update the software on your target. Refer to How to Format Real-Time Target and Reinstall the Software? for directions on how to format and reinstall software on your target. Updating the software patches the Run-Time Mode for the operating system under normal operation. In MAX, expand Software under your target and verify that NI CompactRIO 14.1.1 appears.
- Repeat Steps 3 and 4 for each affected CompactRIO target.
Compact Vision System
You must complete each of the following steps to ensure that any current or future devices have this security update included.
- Verify you have IMAQdx 14.0.0 installed on the host system. IMAQdx 14.0.0 can be found in the Vision Acquisition Software August 2014 release. You can verify that this version has been installed on your host system in Measurement and Automation Explorer (MAX) by expanding Software under My System. You should see IMAQdx 14.0.0. If you do not have IMAQdx 14.0.0, you can obtain it by downloading Vision Acquisition Software August 2014 through update service or from the Related Links section below.
- Install the NI Linux Real-Time Security Update for CVS-1458RT, CVS-1459RT - November 2014 on your host computer. To verify a system has been patched you should see firmware revisions 2.2.0f0 in the corresponding target directory.
- For the CVS-1458RT, the folder location is <Program Files>\National Instruments\Shared\Firmware\CVS\77AA
- For the CVS-1459RT, the folder location is <Program Files> \National Instruments\Shared\Firmware\CVS\76CE
Ensure that you have patched all development systems.
- Update the firmware on your affected controllers.
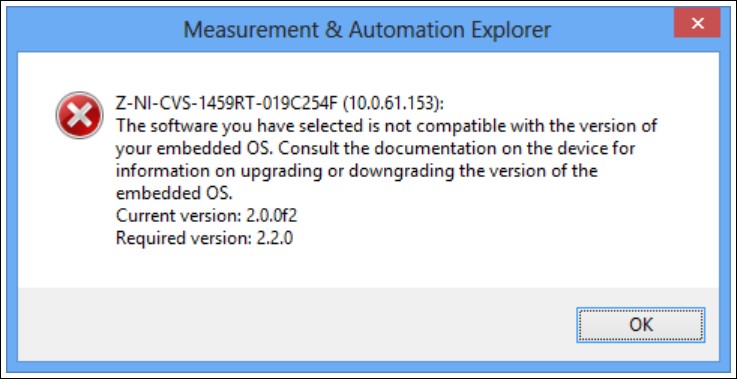
Refer to Upgrading Firmware on my NI Linux Real-Time Device for directions on how to update the firmware on your current controllers. Updating the firmware patches the Safe Mode on the controller so the vulnerability cannot be used while in this mode. In MAX, click the System Settings tab of the controller and verify that Firmware Revision is 2.2.0f0 or later. If this step is skipped you will see the screen shot similar to figure below when proceeding to the next step.
- Update the software on your target. Refer to How to Format Real-Time Target and Reinstall the Software? for directions on how to format and reinstall software on your target. Updating the software patches the run-time mode for the operating system under normal operation.
- Repeat Steps 3 and 4 for each affected Compact Vision System target.
CompactDAQ
You must complete each of the following steps to ensure that any current or future devices have this security update included.
- Verify you have NI-DAQmx 14.2 installed on the host system. You can verify that the update has been installed in Measurement and Automation Explorer (MAX) by expanding Software under My System. You should see NI-DAQmx MAX Configuration 14.2 if the update has been installed successfully. If you do not have the update, you can download the patch through the download page in the related links section.
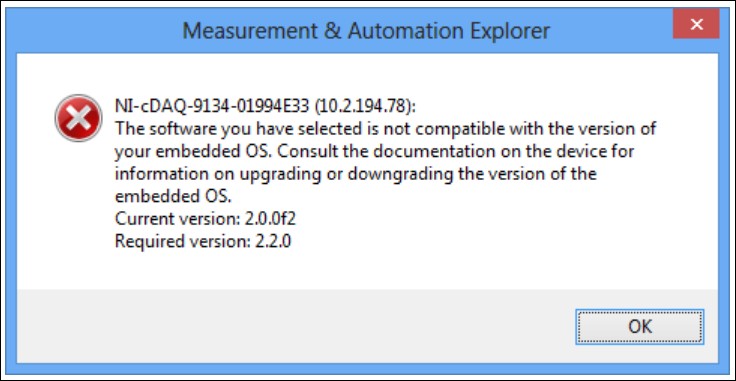
- Update the firmware on your affected controllers. Refer to Upgrading Firmware on my NI Linux Real-Time Device for directions on how to update the firmware on your current controllers. Updating the firmware patches the Safe Mode on the controller so the vulnerability cannot be used while in this mode. In MAX, click the System Settings tab of the controller and verify that Firmware Revision is 2.2.0f0 or later. If this step is skipped you will see the screen shot similar to figure below when proceeding to the next step.
- Update the software on your target. Refer to KnowledgeBase 3O1CE2C5 for directions on how to format and reinstall software on your target. Updating the software patches the run-time mode for the operating system under normal operation. To verify you have the correct software installed on your target, expand Software in MAX under your target. You should see NI-DAQmx 14.2.0.
- Repeat Steps 2 and 3 for each affected CompactDAQ target.
Background
A family of security vulnerabilities, commonly known as "Shellshock," affects Linux distributions that use GNU Bash, including the NI Linux Real-Time operating system. These vulnerabilities allow remote attackers to execute arbitrary code and gain unauthorized access to the system. Exploitation of this vulnerability allows unauthorized disclosure of information, unauthorized modification, and disruption of service. The National Vulnerability Database (NVD), the U.S. government’s repository of standards based vulnerability management data, reported a Common Vulnerability Scoring System (CVSS) base score of 10.0 which is the highest possible severity score.
Patch Details
All NI controllers that run the NI Linux Real-Time operating system are affected by Shellshock. This security update addresses the following reported vulnerabilities:
CVE-2014-6271
CVE-2014-6277
CVE-2014-6278
CVE-2014-7169
CVE-2014-7186
CVE-2014-7187
Follow the steps listed above to install the appropriate software patch.